APP脱壳:梆梆企业版
查壳

启动frida
查看启动app闪退点
frida -U -f com.xxx.xxx -l .\1hook_dlopen.js
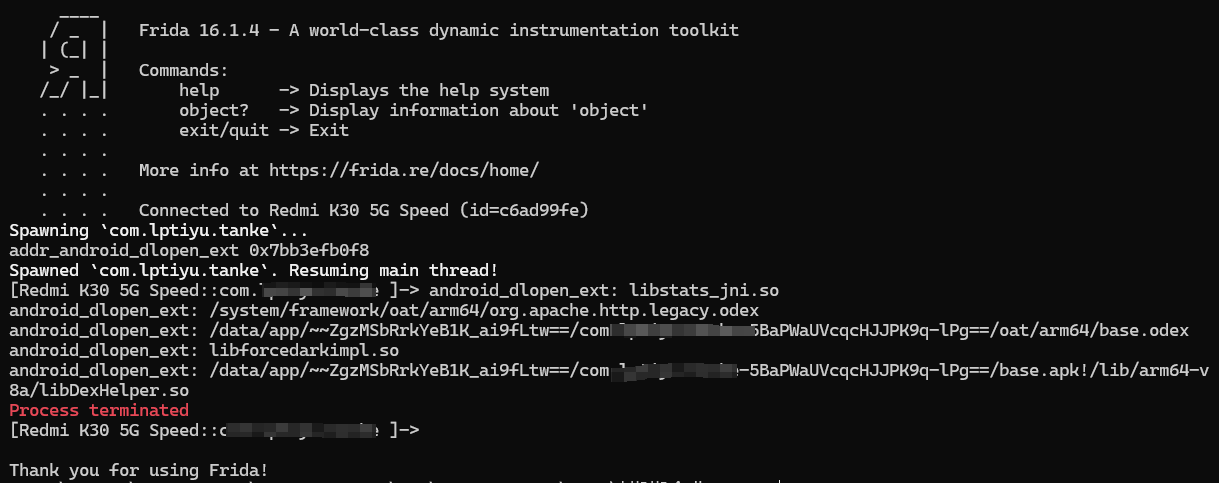
libDexHelper.so 加载后frida退出
找闪退地址
frida -U -f com.xxx.xxx -l .\3hook_remove_findKillAddr.js
发现0x31ec0时frida退出
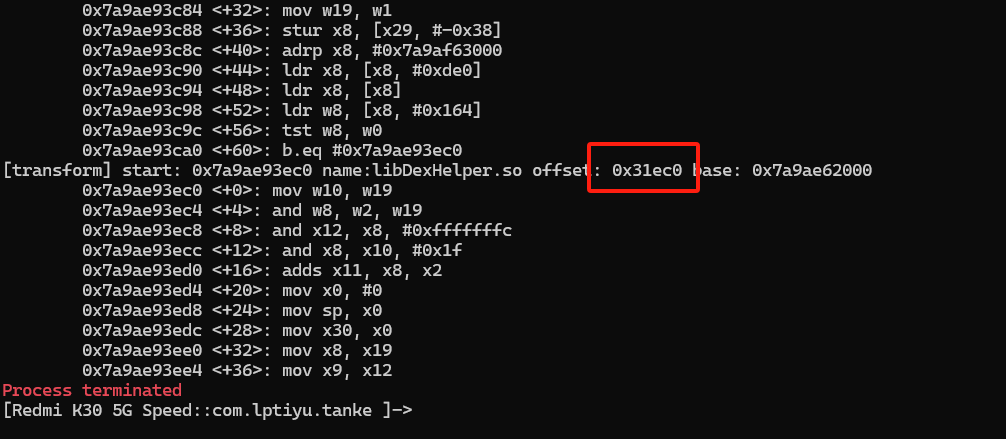
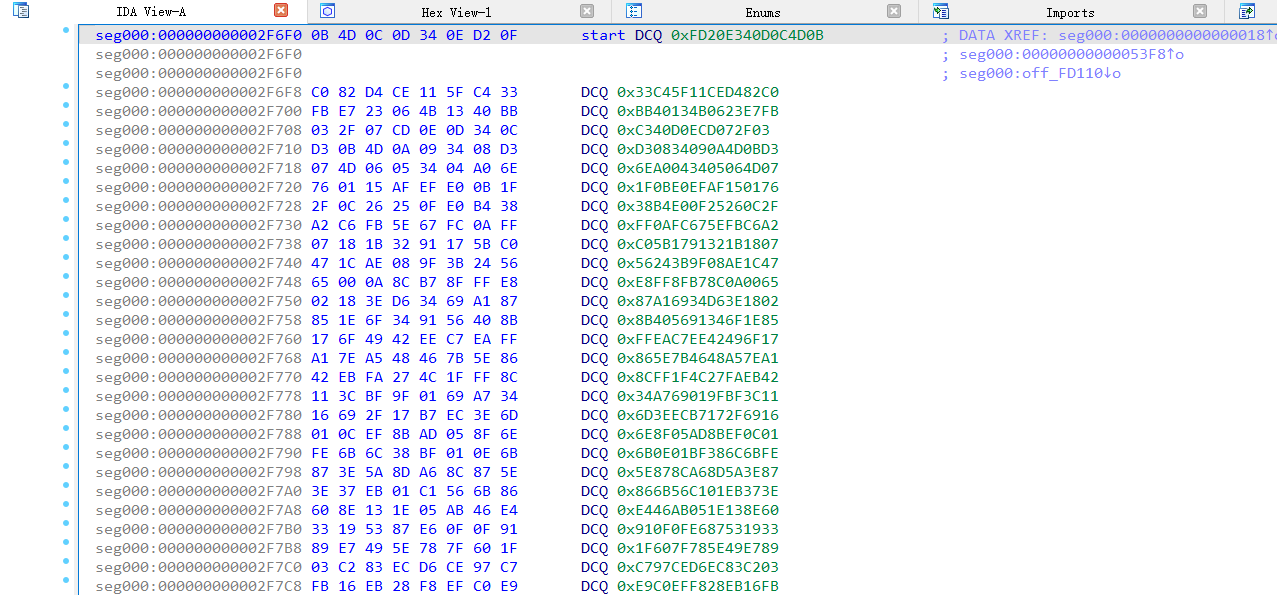
提取libDexHelper.so到IDA里分析,打开发现已混淆
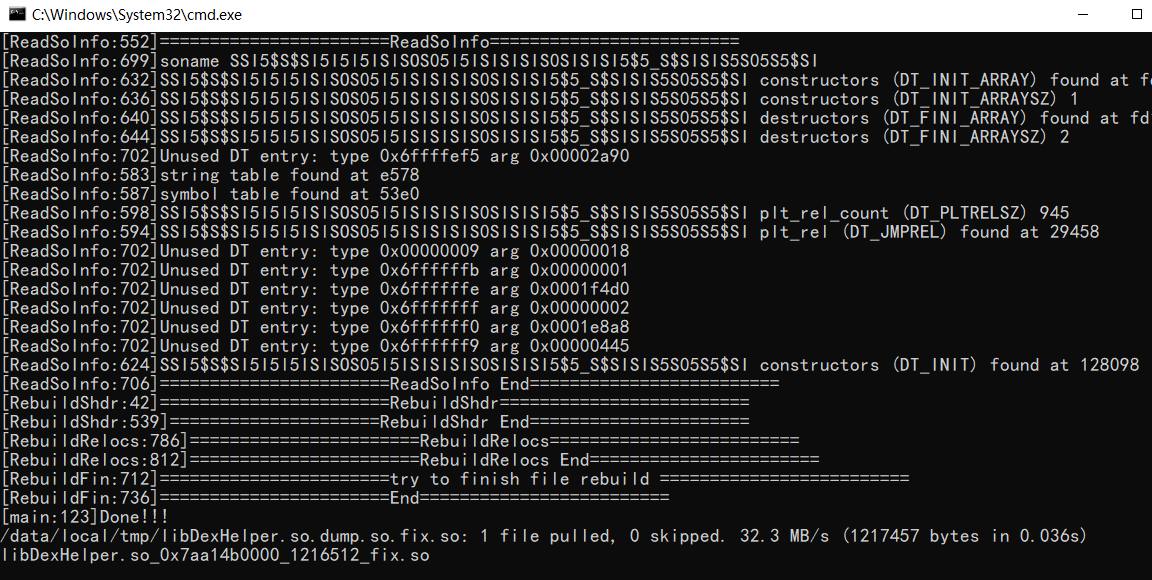
内存dump so解混淆
打开app并执行python3 dump_so.py libDexHelper.so
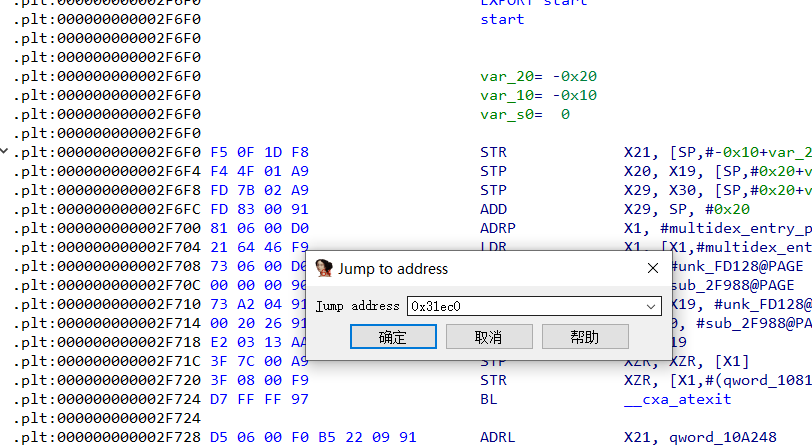
使用IDA打开解混淆的so文件,跳转地址0x31EC0
F5
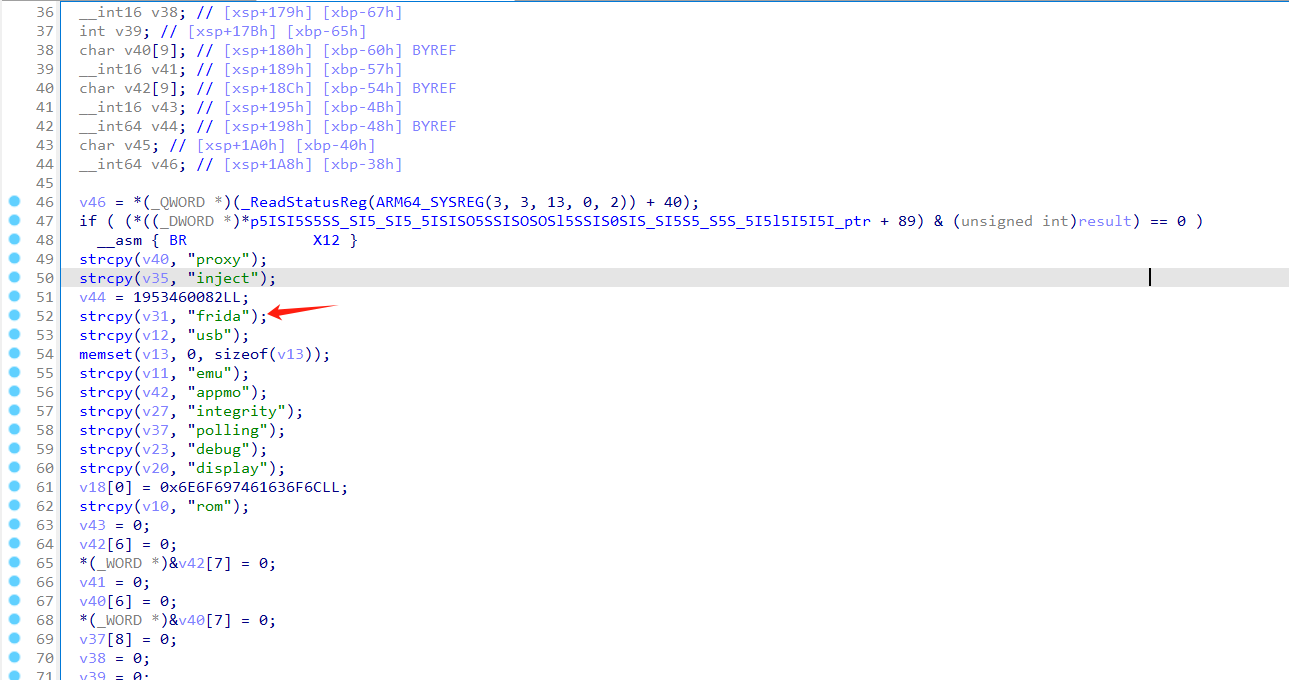
很明显frida关键字,进行nop掉
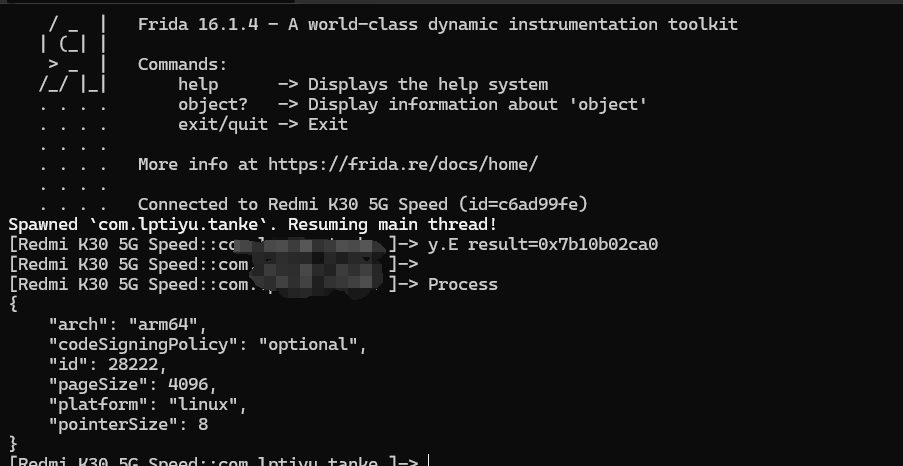
成功绕过frida检测
内存dump dex拿源码
frida -UF -l dexCache_dump.js
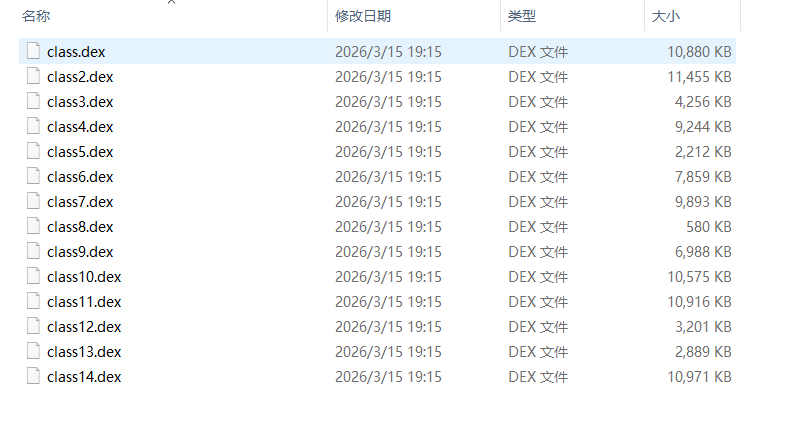
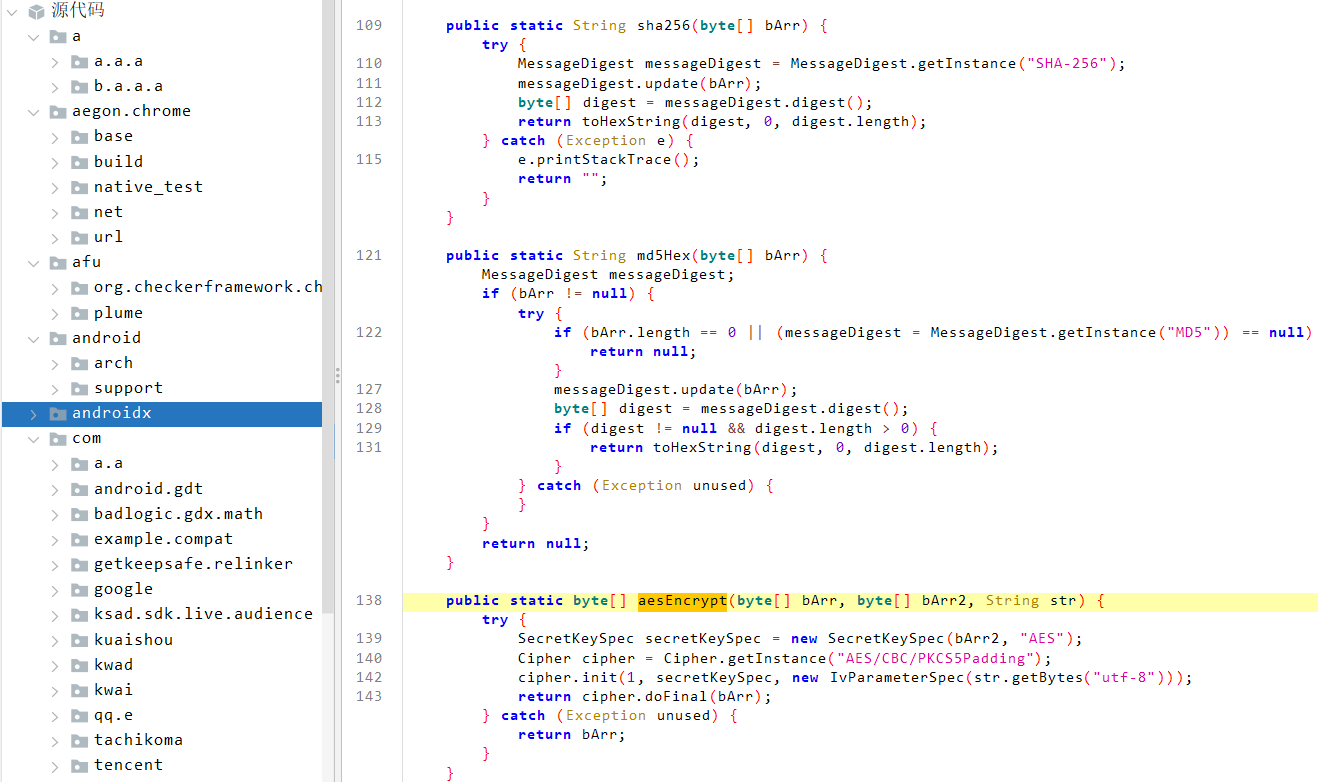
拿到源码,jdax打开愉快的找加解密